The concept of Bring Your Own Device (BYOD) has gained significant popularity among businesses in today’s remote work environment, offering employees the flexibility to use their personal devices for work-related tasks. However, amidst the convenience and cost savings, there are potential risks of BYOD that must be carefully considered before making the jump.
As the Co-Founder of InfoTECH Solutions, Brian Leger, mentions, “BYOD opens the door to a myriad of security vulnerabilities and challenges, leaving sensitive company data exposed to criminals.” This introduces the importance of having a knowledgeable IT partner safeguard your remote work environment from today’s growing BYOD risks.
In this blog post, we will discuss the inherent risks of BYOD and explore the measures that your business can take to mitigate these threats effectively.
Understanding the Trend of BYOD
Companies are increasingly adopting the bring your own device (BYOD) approach to leverage the familiarity and productivity potential of employees’ personal devices. Why?
BYOD allows workers to seamlessly integrate their work and personal lives, enabling them to access critical information and collaborate on projects from anywhere, anytime. It also eliminates the need for employers to provide and manage a fleet of company-owned devices, resulting in significant cost savings.
By embracing BYOD, companies aim to enhance employee satisfaction, productivity, and work-life balance, while simultaneously reducing expenses associated with hardware procurement and maintenance. Consider these BYOD statistics:
- The BYOD market is worth over $80 billion.
- 82% of organizations have a BYOD program.
- 68% of organizations see a jump in productivity after switching to BYOD.
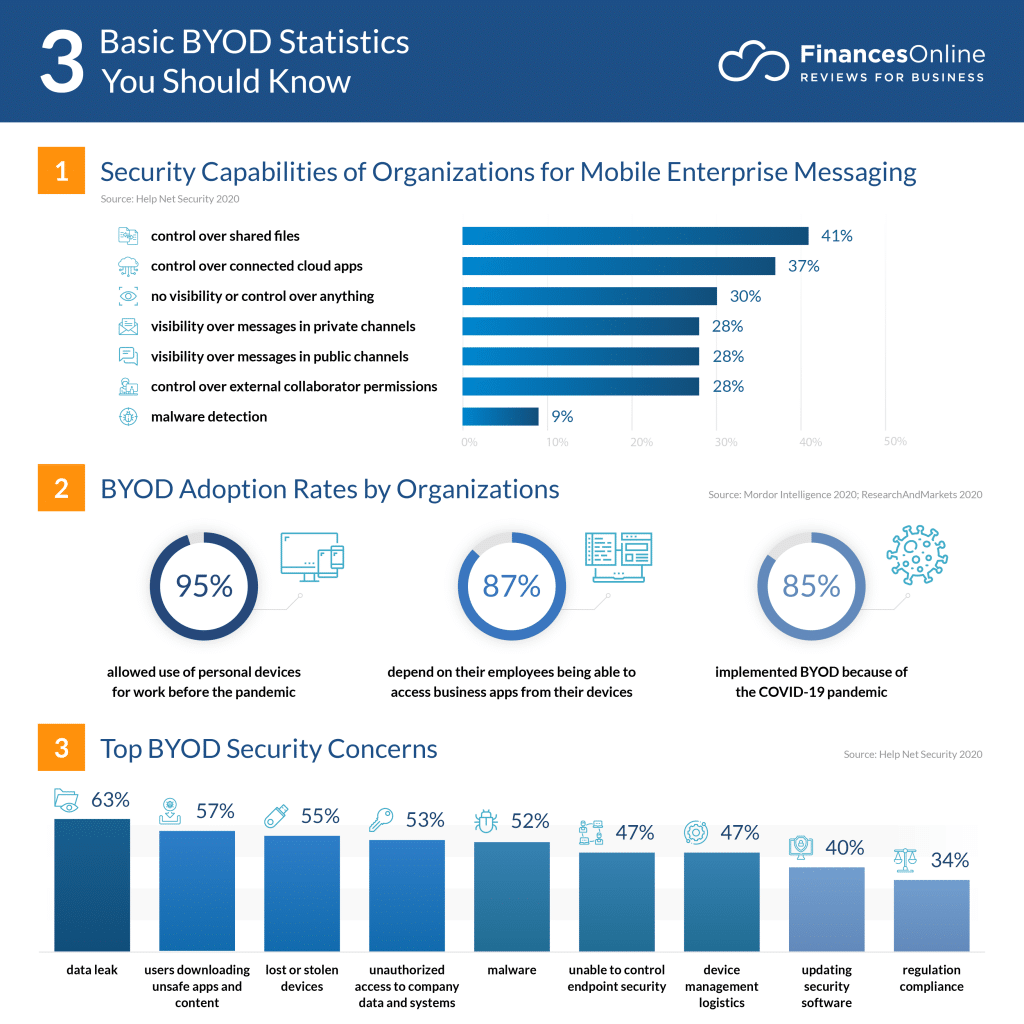
Image Credit: Finances Online
That being said, there are also important BYOD risks and issues that are important to take into account. Let’s take a look at some of the most common security risks of BYOD, and how you can mitigate them effectively.
BYOD Security Risks: What to Look Out For
1. Data Breaches
One of the most common BYOD security risks is the potential for data breaches. Personal devices may lack the same level of security as company-provided devices, making them more vulnerable to cyber threats.
To mitigate this problem with BYOD, partnering with a managed service provider (MSP) can be invaluable. An MSP can implement robust security measures such as data encryption, virtual private networks (VPNs), and multi-factor authentication (MFA) to ensure secure data access and prevent unauthorized access.
Worried About the Security Risks of BYOD?
Stop letting fear hold you back – Learn how we can help
Contact Us Now2. Malware and Viruses
Personal devices are more susceptible to malware and viruses, which can easily spread to the corporate network and compromise sensitive information. An MSP can implement strong antivirus software and regularly update security patches to protect against this security risk of BYOD. Additionally, they can conduct regular device audits to detect and remove any malicious software from employee devices.
3. Lack of Device Management
With BYOD, managing a diverse range of devices and operating systems becomes a challenge for IT teams. MSPs can provide Mobile Device Management (MDM) solutions, enabling centralized control and monitoring of employee devices. MDM allows IT administrators to enforce security policies, remotely wipe data in case of loss or theft, and ensure devices are up to date with the latest security patches.
Navigate Your BYOD Risks and Issues with InfoTECH Solutions:
4. Compliance and Legal Concerns
Depending on the industry, your organization may have specific compliance regulations to adhere to, such as GDPR or HIPAA. BYOD introduces complexities in ensuring compliance and safeguarding sensitive data. An MSP can assist in implementing comprehensive compliance frameworks, ensuring that data protection measures align with relevant regulations. They can also conduct regular audits and risk assessments to identify and address any compliance gaps.
5. Employee Privacy Concerns
BYOD security risks can raise concerns about employee privacy, as companies may have access to personal information on employee-owned devices. To address this, an MSP can help establish clear policies and guidelines that delineate between personal and corporate data.
They can implement containerization techniques, segregating work-related data from personal data, thus preserving employee privacy while still allowing your business to manage and secure corporate information.
By leveraging the expertise of an MSP, companies can proactively mitigate these common BYOD risks, ensuring a secure and compliant environment while harnessing the benefits of employee-owned devices.
Check out these additional resources to learn more:

Say Goodbye to Problems with BYOD with InfoTECH Solutions
In the realm of “bring your own device to work” security issues, placing your trust in a reliable partner like InfoTech is paramount.
With our extensive knowledge and expertise, InfoTECH Solutions is equipped to help you navigate the complex landscape of problems with BYOD and provide tailored solutions to mitigate them effectively.
With us as a trusted partner, you can confidently embrace the advantages of BYOD without compromising security. Get in touch today to learn how we can help you navigate your “bring your own device to work” security issues!